Configure Conditional Access with Veeam 12.3.1
Introduction
Conditional Access policies in Microsoft Entra ID (formerly Azure Active Directory) are critical for enforcing adaptive access controls in your organization. Misconfiguring or losing these policies can lead to serious security risks and operational disruptions.
As of version 12.3.1, Veeam Backup & Replication introduces support for backing up and restoring Conditional Access policies. This adds another layer of resilience to your identity infrastructure by allowing you to recover from unwanted changes or deletions.
This guide walks you through the steps required to enable this functionality. It assumes you already have Microsoft Entra ID backups configured in Veeam and are looking to extend that to include Conditional Access policies.
Process and Testing
Step 1: Enable Conditional Access Backup Support
By default, Conditional Access policy backup and restore is disabled in Veeam. You need to enable it manually:
Registry Configuration
On your Veeam Backup server, add a registry key:
-
Path:
HKEY_LOCAL_MACHINE\SOFTWARE\Veeam\Veeam Backup and Replication -
Key:
EntraIdBackupSupportsConditionalAccessPolicyRestore(DWORD) =1
You can also run this in PowerShell:
New-ItemProperty -Path "HKLM:\SOFTWARE\Veeam\Veeam Backup and Replication" `
-Name "EntraIdBackupSupportsConditionalAccessPolicyRestore" `
-Value 1 -PropertyType DWORD -Force
Step 2: Assign Required Permissions in Microsoft Entra ID
To successfully back up and restore Conditional Access policies, you must assign specific API permissions to the Application Registration used by Veeam.
Identify the Application Registration
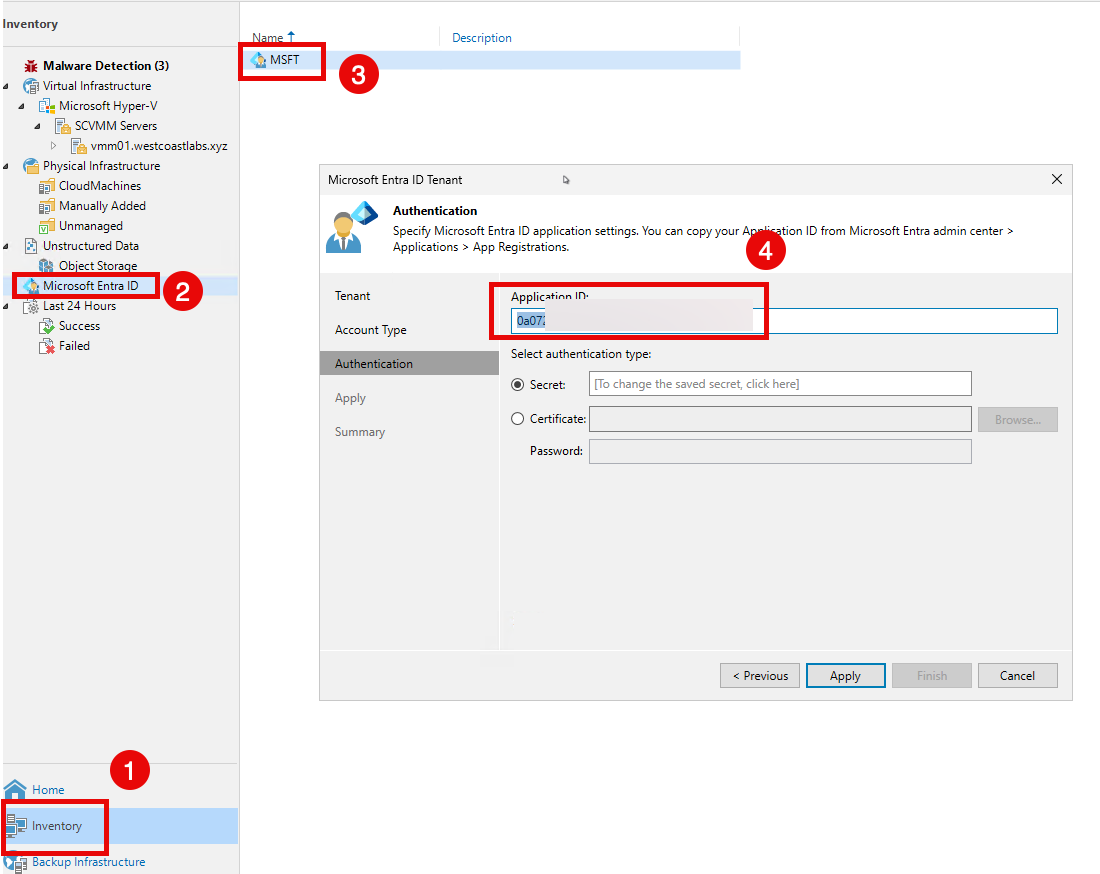
- In Veeam Backup & Replication:
- Go to Inventory → Microsoft Entra ID → Edit.
- Locate the App Registration ID.
- In the Microsoft Entra Admin Center:
- Go to Inventory → Microsoft Entra ID → Edit.
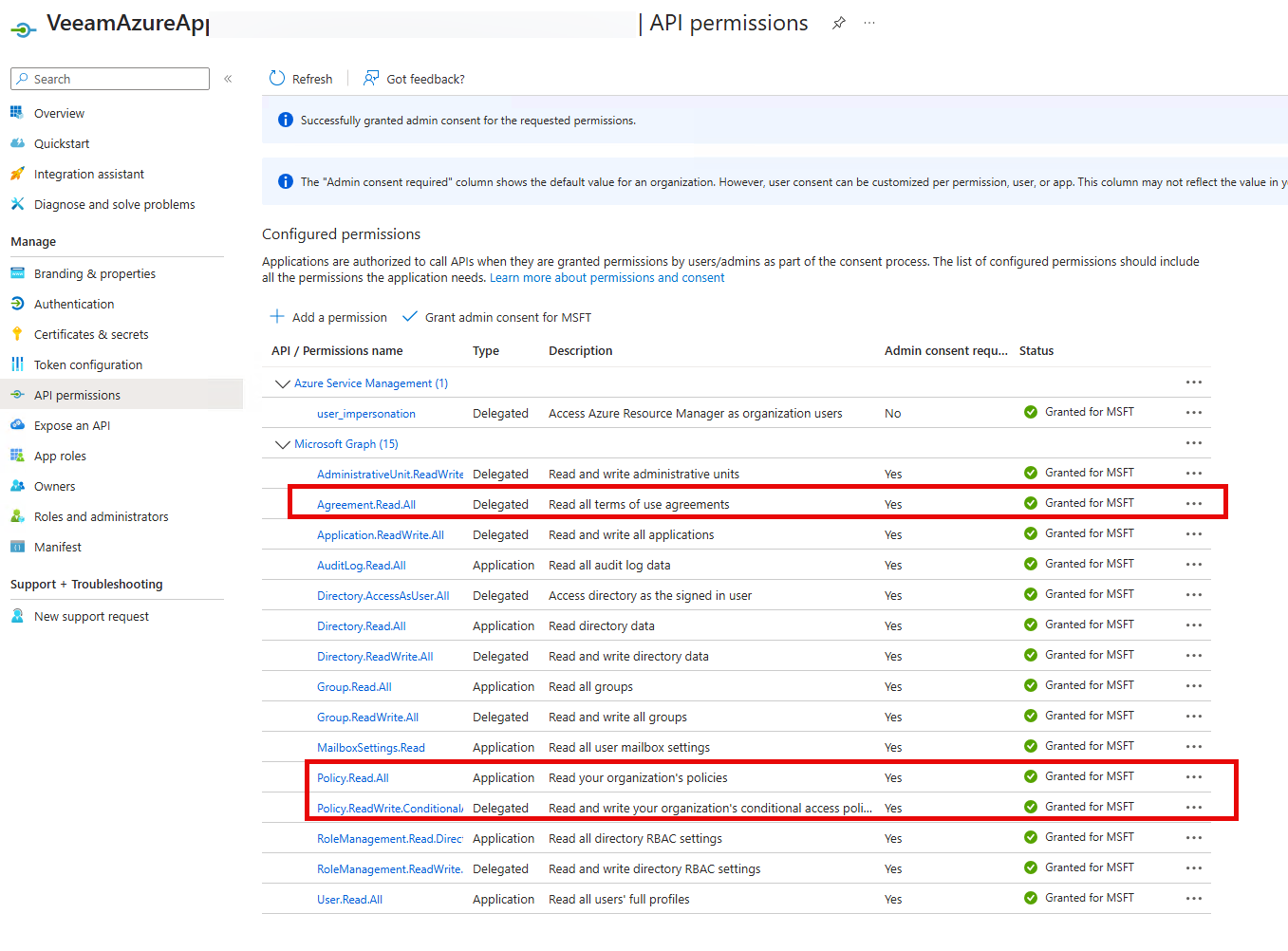
Configure API Permissions
Under API permissions, add the following:
- Application Permissions (used for backup):
- Policy.Read.All – Required to read Conditional Access policies.
- Delegated Permissions (used for restore):
- Policy.ReadWrite.ConditionalAccess – Required to modify Conditional Access policies during restore.
- Agreement.Read.All – Required to access policy-related agreements.
Don’t forget to Grant Admin Consent after adding these permissions.
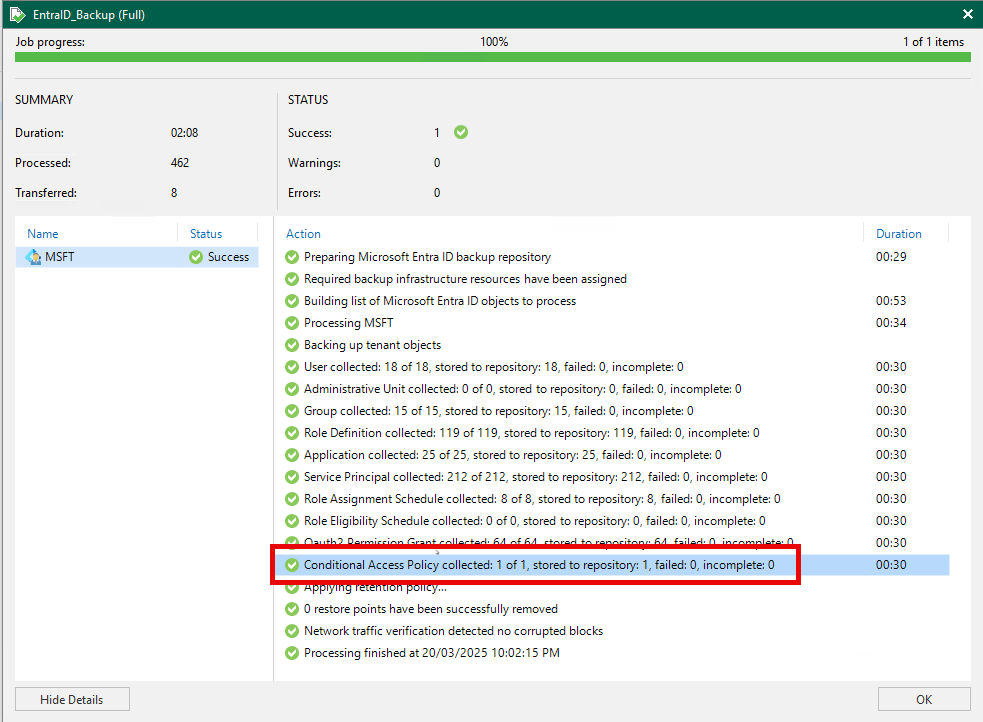
Step 3 Run the EntraID Backup Job
With the registry key and permissions configured, run your Microsoft Entra ID backup job to validate everything is working correctly. You should see no errors or warnings related to Conditional Access in the job summary.
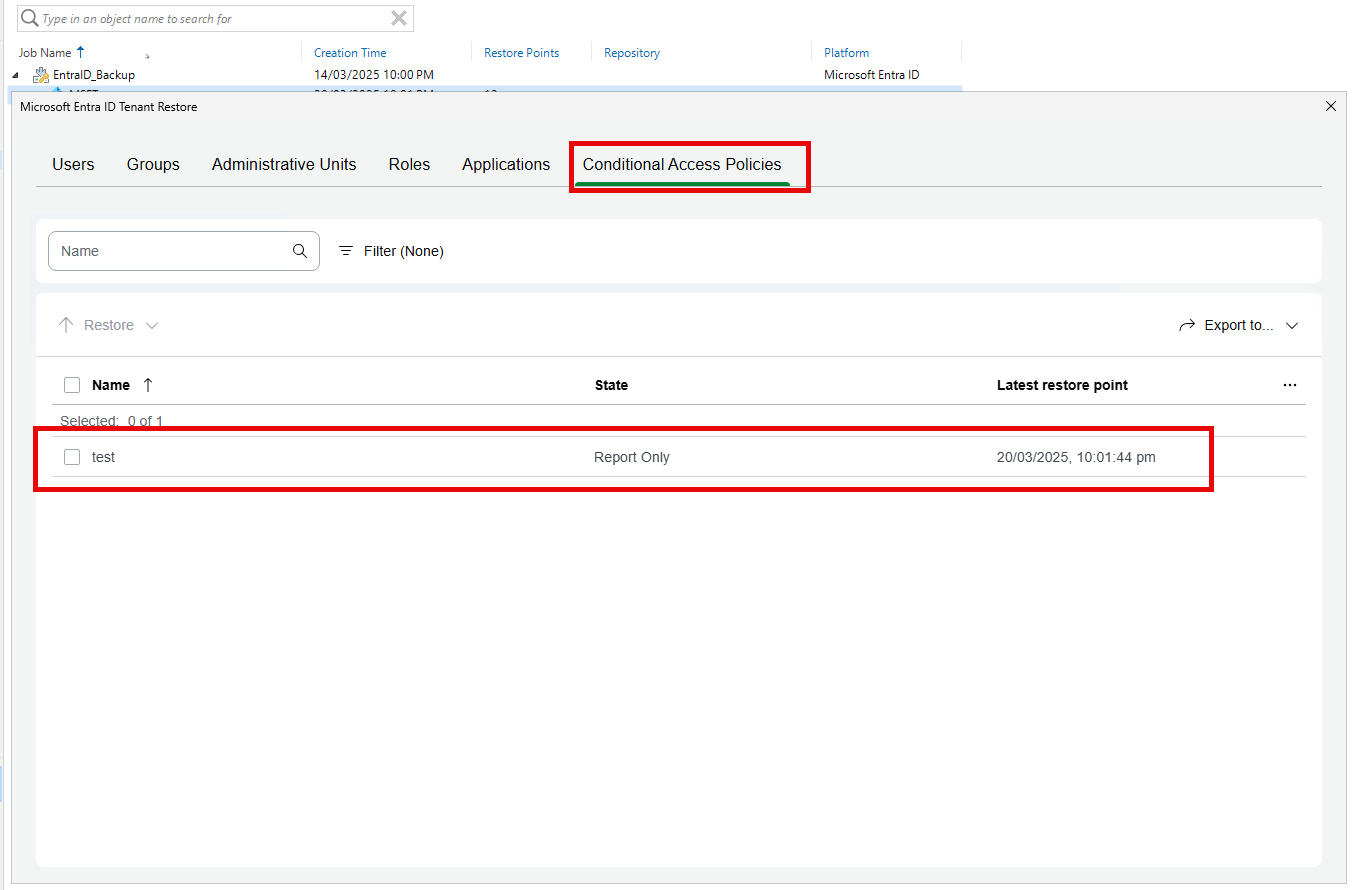
Step 4: Test the Restore Functionality
Backup is only half the story—ensure you can successfully restore Conditional Access policies in a test or non-production environment.
This confirms that the delegated permissions are functioning as expected and that Veeam can write the policy data back into Entra ID
Conclusion
With the release of Veeam Backup & Replication 12.3.1, organizations gain the ability to back up and restore Microsoft Entra Conditional Access policies. This enhancement is crucial for:
- Protecting against accidental deletions or misconfigurations.
- Meeting compliance and audit requirements.
- Improving overall disaster recovery preparedness.
By enabling this feature and assigning the required permissions, you ensure your Conditional Access configurations are just as protected as the rest of your critical infrastructure.
I hope this guide was helpful! As always, keep learning and stay secure!